Search Results for 'Malicious Mail'
Malicious Mail published presentations and documents on DocSlides.
Cine Star Central Spine Vidyadhar Nagar Jaipur Rajasthan India Phone mail m ailaurigaitsolutions
com wwwaurigaitsol utionscom Page 1 of 7 brPage 2b...
PORCELAINGRES GmbH Sitz Irisstrasse Vetschau D Postfach Eingetragen Amtsgericht Cottbus Hrb Cb Tel Fax Mail infopo rcelaingres
com wwwporcelaingrescom Bankverbindung Deutsche Ba...
Chadwicks of Boston Division of Brylane Taunton Massachusetts Chadwicks of Boston is a leading mail order catalog featuring a wide selection of high quality brand name merchandise of ready to wear wo
Chadwicks of Bosto n was in the process of expand...
Starting a Chat Yahoo Mail Classic Page of Starting a Chat You can start chats with your friends whenever you use Yahoo Mail
Just be sure that youre signed in to chat brPage ...
News Finance Entertainment Yahoo My Yahoo Mail My Travel More New User Sign Up Sign In Help Make Y your home page Yahoo Search Overview Hotels Things to do Restaurants Map Flights Cars Deals FareChas
net Sushi Lounge Hoboken NJ Reviews of Sushi Loun...
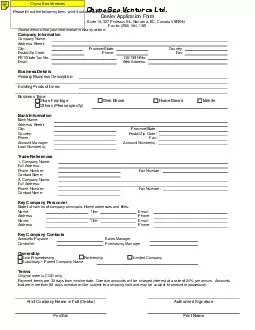
Dealer Application Form Mail to Suite Prideaux St
Nanaimo BC Canada V9R2N4 ax to 250 7401185 Please...
Purse Testimonials One of our favorite testimonials is an unsolicited voice mail message left by a customer after she received her cleaned Gucci bag in the mail
wwwpulitopursecom to listen While at Neiman Marcu...
Sales and Use Tax Division Mail Station St
Paul MN 55146 6330 Phone 651 296 6181 or 1 800 65...
THE COTTON CORPORATION OF INDIA LTD A Government of India Undertaking BhavanarayanNilyam Near JyotiMahal Hotel Convent Road Rayagada Tel No E Mail rayagadacotcorp
com Recruitment of Office Clerk AccountsGeneral on...
Credit repair Save your time and money by knowing the signs of a scam You see credit repair service offerings in newspapers mail flyers on TV or the Internet and hear them on the radio or phone calls
Many make the same claims Credit problems No p ro...
If additional information is needed to process your request the consumer credit reporting company will contact you by mail
Your request will be processed within 15 days of ...
The Story of the Daily Mail Paul Harris Chief News Fea
He hung up his coat in a modest office then worke...
dWt The Daily Mail and the First World War Adrian Bing
The paper had been warning about the German threa...
CLASSIFIED FACT SHEE Daily Mail Saturday Mail on Eveni
6 20 28 23 25 26 Solus readers 2832000 3703000 316...
COMMON MISTAKES OF DIRECT MAIL CAMPAIGNS Avoid ese Co
3210869 21 22 23
Page of The Seamens Church Institute Christmas at Sea For patterns and to read more about SCI visit seamenschurch
org READY TO MAIL Christmas at Sea 118 Export Stre...
GREENSLEEVES RELEASED CHOREO Gert Jan Susie Rotscheid ADDRESS Oude Arnhemseweg BB Zeist The Netherlands PHONE FAX MAIL rotscheidtiscali
nl WEBSITE wwwrotscheidnl MUSIC Greensl eeves CD T...
Westferry Circus Canary Wharf London E HB United Kingdom An agency of the European Union Telephone Facsimil mail infoema
europaeu Website wwwemaeuropaeu European Medicine...
Creating the Daily Mail Historical Archive Seth Cayley Publisher for Media History at Cengage Learning It is self evident that digital archives have transformed the landscape of historical research e
The sheer digital accessibility of rare material ...
SECURITY FREEZE INFORMATION Any consumer in Illinois may place a security fre eze on his or her credit report by requesting one in writing by certified mail to the consumer reporting agency
The consumer reporting agency is not allowed to c...
Accessing Your TRS Account Online U
S Mail or email You also can call TRS at 800 87778...
Italian Catholic Federation Capwell Drive Suite Oakland CA Fax infoicf
org E mail wwwicforg Web site The Italian Catholi ...
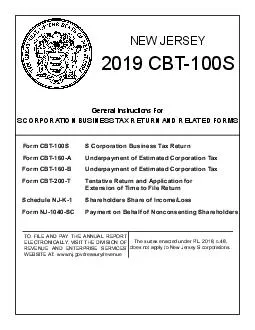
CBTS MAIL COMPLETED CBTS TO STATE OF NEW JERSEY DEPARTMENT OF THE TREASURY DIVISION OF TAXATION REVENUE PROCESSING CENTER POBOX TRENTON NJ Form CBTS S Corporation Business TaxReturn Form CBTSV Pay
njgovtreasuryrevenue S CORPORATION BUSINESS TAX RE...
Westferry Circus Canary Wharf London E HB United Kingdom An agency of the European Union Telephone Facsimile mail infoema
europaeu Website wwwemaeuropaeu European Medicine...
Sales and Use Tax Division Mail Station St
Paul MN 551466330 Phone 6512966181 or 18006573777...
If your business thrives on creating relationships direct mail may be the best choice to lead your contact strategy
LYL57347HYL5734757540L57347YLHZVUZ57347O57347KPYL...
MacSchool Digital Arts and Programming Centre Tel
015642 66376506 Mail infomacschoolcommx wwwmacscho...
Clearpath Federal Credit Union Contact Info Contact the Credit Union mail infoClearpathfcu
org General questions and information Please do no...
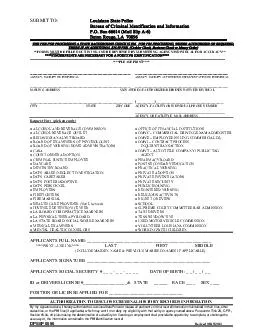
SUBMIT TO Louisiana State Police Bureau of Criminal Identification and Information P
O Box 66614 Mail Slip A 6 Baton Rouge LA 70896 THE...
CMGT Copywriting and Creativity Fall Monday pm Instructor Gary Wexler mail gwexlerusc
edu Office To be determined Office hours Mondays 5...
Office of the Registrar Course AddDrop Form OTE ude ID Semeste r ame Last Mobile Phone Mail ddre ss Da Instructions An instructors signature is required to add a closed course override a pre requisit
Once completed this orm must be submitted to the ...
A stepbystep guide to help you plan and create your next direct mail campaign
wwwcanadapostca Canada Post Direct Mail Campaign ...
DMM USPS Page Effective December Quick Service Guide Additional Services Business Reply Mail Related QSGs c Courtesy Reply Mail CRM e Meter Reply Mail MRM Overview For an annual permit fee a Bus
Business Reply Mail BRM service enables a permit ...
Westferry Circus Canary Wharf London E HB United Kingdom An agency of the European Union Telephone Facsimile mail press ema
europaeu Website wwwemaeuropaeu 19 March 2014 EMA4...
Discrete Chebyshev Classiers Elad Eban ELADE CS HUJI AC IL Elad Mezuman ELAD MEZUMAN MAIL HUJI AC IL Amir Globerson GAMIR CS HUJI AC IL Edmond and Lily Safra Center for Brain Sciences
The Hebrew University of Jerusalem The Selim and ...
Lower Plenty Road YALLAMBIE VIC Phone Fax mail infoarpansa
govau Web wwwarpansagovau Freecall 1800 022 333 a ...
Residential Mail Procedures Residential Mail Services Owens Hall Rm Kent Street Blacksburg VA Phone mailservicesvt
edu Hours 800 am 500pm Monday through Friday wwwma...
This research has been supported by CICYT TIC and TICC
Corresponding author mail address ocordon decsai...
ISSN Print Volume Issue Performance of Indirectly Controlled STATCOM with IEEE bus System Jagdish Kumar Department of Electrical Engineering PEC University of Technology Chandigarh India mail
com Abstract STATCOM is one of the Flexible AC Tra...