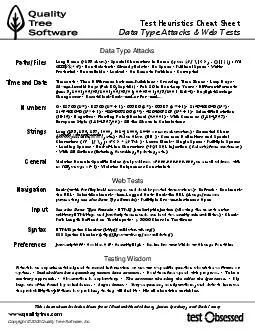
PDF- Data Type Attacks Web Tests Testing Wisdom
57463574635746357390574575746157441574525744957460574655746057458574455744557390574435745557453 574285744857449574595737657443574485744557441574605737657459574485744557445574605737657449574545744357452574615744457445574595737657449574445744557441574
Download Presentation
" Data Type Attacks …" is the property of its rightful owner. Permission is granted to download and print materials on this website for personal, non-commercial use only, provided you retain all copyright notices. By downloading content from our website, you accept the terms of this agreement.
Presentation Transcript
Transcript not available.