PPT-Staying safe in a digital age
Author : blackwidownissan | Published Date : 2020-08-26
1Have a strong password A t least 10 characters long 12 for IOM3 A mixture of numbers uppercase and lowercase letters Include other symbols Avoid common words Do
Presentation Embed Code
Download Presentation
Download Presentation The PPT/PDF document "Staying safe in a digital age" is the property of its rightful owner. Permission is granted to download and print the materials on this website for personal, non-commercial use only, and to display it on your personal computer provided you do not modify the materials and that you retain all copyright notices contained in the materials. By downloading content from our website, you accept the terms of this agreement.
Staying safe in a digital age: Transcript
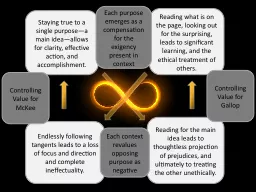
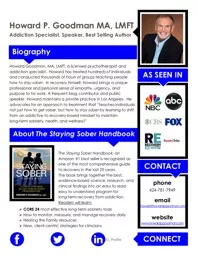
1Have a strong password A t least 10 characters long 12 for IOM3 A mixture of numbers uppercase and lowercase letters Include other symbols Avoid common words Do not reuse passwords Change your password regularly. We have no digital cable boxes that will work on digital cable tv No digital cable box is available Digital cable descrambler and digital cable box will be available someday At this time no digital cable tv box is available Look for digital cable de Staying Safe Online. 11-16 . Staying Safe Online 11-16 . My social network?. Learning outcomes. All . students will . be able to . explore notions of ‘friends’ and ‘privacy’ by creating a proportional diagram showing their different types of friends. Welcome. We value partnering with you to maintain a safe . TU. community. Your safety is a shared responsibility . and our primary concern. Campus Safety Services is composed . of . many dedicated and highly skilled . Lesson Objectives. In this lesson, you will:. Identify ways to keep safe online.. Minimise risk and harm in online communities.. Think about ways to advise other pupils on how to conduct themselves online.. Staying Strong . When Things Go Wrong. 2. (Reuters) - . Thu May 26, 2011 3:17pm EDT. More than 500 people have been killed by twisters in 2011, . . . As of mid-Thursday, 505 people had died in tornadoes this year, including at least 123 who died as a direct result of the monster storm that tore through Joplin, Missouri, on Sunday. . . The National Weather Service reported another 17 deaths this week in Oklahoma, Kansas and Arkansas . . .The total makes 2011 the seventh-deadliest tornado year on record in the U.S. and inches it closer to the 519 deaths recorded in 1953.. Path, Part 2. 1 John 2:15-17. The Basis of Our Fellowship . (2:12-14). :. The . F. orgiveness. of O. ur. S. ins. – for H. is. N. ame’s. . S. ake. !. An . I. ntimate. K. nowledge. of Our . G. Safe . Online. . Cork Educate Together . National School. November 2014. The Internet/. World Wide Web. The Internet and the connections it allows us to make all over world is a wonderful tool for:. STAYING POSITIVE IN A NEGATIVE WORLD. Dealing with Murmuring. STAYING POSITIVE IN A NEGATIVE WORLD. There is a time and a method for. . expressing legitimate concerns.. Dealing with Murmuring. STAYING POSITIVE IN A NEGATIVE WORLD. Reading what is on the page, looking out for the surprising, leads to significant learning, and the ethical treatment of others.. Reading for the main idea leads to thoughtless projection of prejudices, and ultimately to treating the other unethically.. Staying Away From the . MirY. . ClAY. Pride – The Root?. PRIDE: DEFINITIONS AND CHARACTERISTICS. What does Bible mean when talking about pride in a negative sense? Includes:. Arrogance. Insensitivity to needs of others. Biography. Howard Goodman, MA, LMFT, a licensed psychotherapist and addiction specialist. Howard has treated hundreds of individuals and conducted thousands of hours of groups teaching . people how . BEWARE OF MOSQUITULA!. Egg Raft. Larva. Pupa. Adult. Warmth. Blood. Nectar. Producers. Consumers. Wetland Ecosystem. Backyard. Ecosystem. Blood. Saliva . pathogens (virus). Blood-feeding. West Nile Virus, etc.. Staying Put in New Canaan. STAYING PUT. SAFELY BEHIND THE WHEEL. Older Drivers Are At Greater Risk of Injury and Death in an Auto Accident. How Does Age Affect Driving?. Vision. Gradually deteriorates over time. Alcohol and Pregnancy. No safe amount. No safe time. No safe alcohol. Period. Neuropsychology of Fetal Alcohol Syndrome: Methods and Findings Anne Uecker PhD Child Neuropsychologist Edmund N
Download Rules Of Document
"Staying safe in a digital age"The content belongs to its owner. You may download and print it for personal use, without modification, and keep all copyright notices. By downloading, you agree to these terms.
Related Documents