PDF-ApsycholinguisticperspectiveontheacquisitionofphonologyFranckRamus,Sha
Author : calandra-battersby | Published Date : 2015-10-01
FranckRamusetalthelatterisamoredetailedlevelofrepresentationinwhichcompleteutterancesarerepresentedasasequenceofspeechsoundsorphonesThephonologicalgrammarmediatesbetweenthesetwolevelsinthatitmapsun
Presentation Embed Code
Download Presentation
Download Presentation The PPT/PDF document "Apsycholinguisticperspectiveontheacquisi..." is the property of its rightful owner. Permission is granted to download and print the materials on this website for personal, non-commercial use only, and to display it on your personal computer provided you do not modify the materials and that you retain all copyright notices contained in the materials. By downloading content from our website, you accept the terms of this agreement.
ApsycholinguisticperspectiveontheacquisitionofphonologyFranckRamus,Sha: Transcript
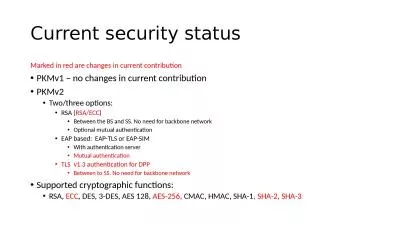
FranckRamusetalthelatterisamoredetailedlevelofrepresentationinwhichcompleteutterancesarerepresentedasasequenceofspeechsoundsorphonesThephonologicalgrammarmediatesbetweenthesetwolevelsinthatitmapsun. T op tim ze the energ flow a global optim ization algorithm based on the Bellman prin cipl e was used to generate the st efficient operating con itions for a parallel pretransm ission hybr id and a specific driving cy cle Several driving cy cles wer to Modern Cryptography and State-of-the-Art . Solutions. Kenny Paterson. Information Security Group. Living with the Threat of the Crypt-Apocalypse. Kenny Paterson. Information Security Group. Crypto In Use. Hashing!. Hashing. Group Activity 1:. Take the message you were given, and create your own . version of hashing.. You can . hash it . anyway you want. Try to make an interesting version that you think no other group will be able to guess. FranckRamusetal.thelatterisamoredetailedlevelofrepresentationinwhichcompleteutterancesarerepresentedasasequenceofspeechsoundsorphones.Thephonologicalgrammarmediatesbetweenthesetwolevels,inthatitmapsun NetInf. Jeff Thompson. ICNRG meeting @ IETF-88. November 3, 2013. The sites who say “. ni. !”. November 3, 2013. Firefox Extension for NetInf - Jeff Thompson. 2. Overview. Introduction. Apache support. By – . Debanjan. . Sadhya. (iwc2011013). Mayank. . Swarnkar. (iwc2011026). Contents. Introduction. Definition. Properties of SHA. SHA Functions. SHA Constants. Preprocessing in SHA. Hashing in SHA. Cyryptocurrency Project Proposal - Spring 2015. SHA Use in Bitcoin. SHA256 used heavily as bitcoin’s underlying cryptographic hashing function. Two examples (of many) are its use in the Merkle tree hash, as well as the proof of work calculation. Web. FTP. Email. DNS. P2P. DHT. Distributed Hash Table (DHT). DHT: distributed P2P database. Distributed (why?). Each node knows little information. Low computational/memory overhead. Reliable. database has . Floor Reconfiguration. Construction Management at Risk (CMAR) Project. . INFORMATIONAL MEETING. May . 30. , 2018. SOC Floor Reconfiguration Project Overview. Construction Management at Risk Project Delivery Overview. d. raft-chen-rtgwg-key-table-yang-00. Goals. YANG data model for configuring cryptographic keys for routing protocols. Based on key table defined in RFC 7210. Conceptual key database. Accommodates different key management implementations. Garbhavakranti. (. Fertilization and developmental factors. ). Pres. ented . By . Dr. . Hidayatulla. khan A. . Pathan. . . ASSISTANT PROFESSOR,. DEPARTMENT OF BASIC PRINCIPLES,. SMVVS,. RKMAMCH PG&RC. Solutions. Kenny Paterson. Information Security Group. Living with the Threat of the Crypt-Apocalypse. Kenny Paterson. Information Security Group. Crypto In Use. Relative to the number of primitives that have been invented by academic cryptographers, the number that are . Marked in red are changes in current contribution. PKMv1 – no changes in current contribution. PKMv2. Two/three options:. RSA (. RSA/ECC. ). Between the BS and SS. No need for backbone network. Optional mutual authentication. (IHA) Provider Training. Quality Management Department . November 2022. 2. Learning Objectives. What is the Initial Health Assessment (IHA): Slides 3-4. Provider: IHA timeframe for appointment. : Slide 5.
Download Document
Here is the link to download the presentation.
"ApsycholinguisticperspectiveontheacquisitionofphonologyFranckRamus,Sha"The content belongs to its owner. You may download and print it for personal use, without modification, and keep all copyright notices. By downloading, you agree to these terms.
Related Documents