PDF-(EBOOK)-The Practice of Network Security Monitoring: Understanding Incident Detection
Author : edonosinachi_book | Published Date : 2023-05-20
The Benefits of Reading BooksMost people read to read and the benefits of reading are surplus But what are the benefits of reading Keep reading to find out how reading
Presentation Embed Code
Download Presentation
Download Presentation The PPT/PDF document "(EBOOK)-The Practice of Network Security..." is the property of its rightful owner. Permission is granted to download and print the materials on this website for personal, non-commercial use only, and to display it on your personal computer provided you do not modify the materials and that you retain all copyright notices contained in the materials. By downloading content from our website, you accept the terms of this agreement.
(EBOOK)-The Practice of Network Security Monitoring: Understanding Incident Detection: Transcript
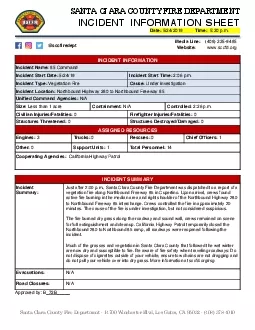
The Benefits of Reading BooksMost people read to read and the benefits of reading are surplus But what are the benefits of reading Keep reading to find out how reading will help you and may even add years to your lifeThe Benefits of Reading BooksWhat are the benefits of reading you ask Down below we have listed some of the most common benefits and ones that you will definitely enjoy along with the new adventures provided by the novel you choose to readExercise the Brain by Reading When you read your brain gets a workout You have to remember the various characters settings plots and retain that information throughout the book Your brain is doing a lot of work and you dont even realize it Which makes it the perfect exercise. On-line . Particle Monitors. Joe Zimmerman. Chemtrac. Systems, Inc.. Norcross, GA. Introduction. The goal of CPT monitoring is to determine:. when corrosion is occurring. where corrosion is occurring. Intruders. Classes (from [ANDE80]:. two most publicized threats to security are malware and intruders. generally referred to as a . hacker. or . cracker. Examples of Intrusion. remote root compromise. Are You Prepared to Respond to a Disaster or Incident?. M. Bernard, . FEMA . Region X . Bothell. , WA; . 05/07/2013. NIMS and the Incident Safety Officer. NRF/NIMS . Coordination Structures. Joint Field Office. . Sponsored by:. Presented by:. Curtis Johnson. LogRhythm Sales Engineer. The Expanding Cyber . Threat . Motive. Political. Ideological. Criminal. Damaging Data Breaches. 40 Million. Credit Cards Stolen. Lesson 20. Computer Crime. The corporate world is beginning to understand that computers are just another medium for crime.. According to the 1999 CSI/FBI survey. average bank robbery yields $2,500. average computer crime nets $500,000. Overview. 2. Identify the major components of dealing with an incident . Understand the incident handling lifecycle. Prepare a basic policy outlining a methodology for the handling of an incident. Report . Windows Event Forwarding – Centralized logging for everyone!. INF327. Logging :. The hardest simplest thing. . Venn Diagram of . Common Monitoring . Strategies. Very few/None of the things. All the things!!!!!!. What is an AIRE?. A focused training activity that places the participants in a simulated situation requiring them to function in the capacity that would be expected of them in a real aircraft mishap or accident.. modified from slides of . Lawrie. Brown. Classes of Intruders – Cyber Criminals. Individuals or members of an organized crime group with a goal of financial reward. Their activities may include: . UTSA IS 6353 Security Incident Response. Overview. Detection of Incidents. Basic IDS Theory. Types of IDSes. UTSA IS 6353 Security Incident Response. What is an Incident?. Incident. - an event in an information . La gamme de thé MORPHEE vise toute générations recherchant le sommeil paisible tant désiré et non procuré par tout types de médicaments. Essentiellement composé de feuille de morphine, ce thé vous assurera d’un rétablissement digne d’un voyage sur . Jo Miller, Senior project officer. Incident Response Team. Nathan Farrow. Manager, Incident Response Team. T. 03 9096 5426. M. 0409 552 986. E. nathan.farrow@dhhs.vic.gov.au. Joanne Miller. Senior Project. Controlled 226pm Civilian Injuries/Fatalities 0 FirefighteralongNorthbound Freeway 85 in Cupertino Upon arrival crews found active fire burningappronvestigation but not consideredsuspicious Thefire b SecOps Solutions Team. Customer Presentation . Agenda. Packages – What | Why. Business Challenges & Solutions. Market Opportunity. Solution Package Summary. Package Description – Value Proposition, Deployment.
Download Document
Here is the link to download the presentation.
"(EBOOK)-The Practice of Network Security Monitoring: Understanding Incident Detection"The content belongs to its owner. You may download and print it for personal use, without modification, and keep all copyright notices. By downloading, you agree to these terms.
Related Documents