PDF-(DOWNLOAD)-CyRM: Mastering the Management of Cybersecurity (Security, Audit and Leadership
Author : trevonyamen_book | Published Date : 2023-05-19
The Benefits of Reading BooksMost people read to read and the benefits of reading are surplus But what are the benefits of reading Keep reading to find out how reading
Presentation Embed Code
Download Presentation
Download Presentation The PPT/PDF document "(DOWNLOAD)-CyRM: Mastering the Managemen..." is the property of its rightful owner. Permission is granted to download and print the materials on this website for personal, non-commercial use only, and to display it on your personal computer provided you do not modify the materials and that you retain all copyright notices contained in the materials. By downloading content from our website, you accept the terms of this agreement.
(DOWNLOAD)-CyRM: Mastering the Management of Cybersecurity (Security, Audit and Leadership: Transcript
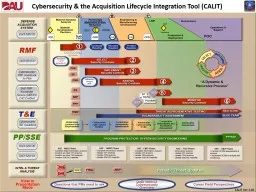
The Benefits of Reading BooksMost people read to read and the benefits of reading are surplus But what are the benefits of reading Keep reading to find out how reading will help you and may even add years to your lifeThe Benefits of Reading BooksWhat are the benefits of reading you ask Down below we have listed some of the most common benefits and ones that you will definitely enjoy along with the new adventures provided by the novel you choose to readExercise the Brain by Reading When you read your brain gets a workout You have to remember the various characters settings plots and retain that information throughout the book Your brain is doing a lot of work and you dont even realize it Which makes it the perfect exercise. CYBERSECURITY BASICS. Overview. CYBERTHREATS. First, let’s talk about some common cyber safety threats and the problems they can cause.. CYBERTHREATS. CONSEQUENCES. Defense against cybersecurity threats requires your action. If you do nothing. . Association . of Corporate Counsel. © 2015. 1. Our . questions…. 2. "What should my company do to prepare for a data-related . incident?". "What can I do to . help manage risks while supporting innovation?”. Workshop. Xenia Mountrouidou (Dr. X). Outline. Motivation. Cybersecurity & Liberal Arts . Cyber Paths. Liberal Arts. GENI . Motivation: Cybersecurity Education. Challenges. Cybersecurity: fast paced, changing field. October 27-28. th. , 2015. Chicago IIA Chapter’s 2. nd. Annual IIA Chicago IT Hacking Conference. Who is . KirkpatrickPrice. ?. KirkpatrickPrice is a licensed CPA firm, providing assurance . services to . CALIT . Ver. 3.1 . Sep 2018. Program Management and Component Actions to Implement . Cybersecurity . Across the Acquisition Lifecycle. Prior to materiel Development Decision (MDD):. Request Cyber threat information and use threat assessments to inform Cyber protection . Cybersecurity Indiana Department of Insurance Financial Services Division Impact on Regulatory Examinations Jerry Ehlers Examinations Manager Indiana Department of Insurance October 25, 2018 Topics How Did We Get Here? Cybersecurity and the Connected Home Recognizing the risk, adopting best practices, harnessing the potential Rawlson O’Neil King CABA Communications Director About CABA Vision CABA advances the connected home and intelligent buildings sectors. 17 October 2017. Presented by:. RDML Ron Fritzemeier. Chief Engineer. Space and Naval Warfare Systems Command (SPAWAR). The overall classification of this brief is: UNCLASSIFIED//FOUO. Presented . to:. IBM Security Software Sales Leader . Burak . Özgirgin. CISSP-ISSAP, CISM, CISA, CEH, ISO27001LA. IBM Security Services – Managing Consultant. Source: IBM X-Force Threat Intelligence Quarterly – 1Q 2015. CALIT . Ver. 2.02. Program Management and Component Actions to Implement Cybersecurity Across the Acquisition Lifecycle. Prior to Material Development Decision (MDD):. Request Cyber threat information and use threat assessments to inform Cyber protection . *A proven system of teaching for teachers, parents, and students who want to learn on their own.*Requires only 20 minutes per day.*Presented in a simple format that everyone can understand.*Each lesson flows smoothly and logically to the next.*Each lesson is short, concise, and straight to the point.*Each new topic is clearly explained.*Lots of examples with step-by-step solutions.*Each lesson includes valuable helpful hints.*Review is built into each lesson. Students will retain what they have learned.*Each lesson includes Problem Solving. This ensures that students will learn to apply their knowledge to real-life situations.*Includes a How to Use This Book section, and an easy-to-use answer key. Suzanne B. Schwartz, MD, MBA. Associate Director for Science & Strategic Partnerships. Office of the Center Director. Center for devices & Radiological Health. October 19, 2016. www.fda.gov. Agenda. agenda. Who . is ISACA. What does ISACA bring to the table. INTOSAI / ISACA Opportunities. Background. Who Are We?. Nonprofit IT Professional membership association founded in 1969. Over 140,000 professionals, 220 chapters in 180 countries. Get complete detail on Cybersecurity Fundamentals exam guide to crack ISACA Certified Cybersecurity Fundamentals. You can collect all information on Cybersecurity Fundamentals tutorial, practice test, books, study material, exam questions, and syllabus. Firm your knowledge on ISACA Certified Cybersecurity Fundamentals and get ready to crack Cybersecurity Fundamentals certification. Explore all information on Cybersecurity Fundamentals exam with number of questions, passing percentage and time duration to complete test.
Download Rules Of Document
"(DOWNLOAD)-CyRM: Mastering the Management of Cybersecurity (Security, Audit and Leadership"The content belongs to its owner. You may download and print it for personal use, without modification, and keep all copyright notices. By downloading, you agree to these terms.
Related Documents







![[EPUB] - Mastering Essential Math Skills Problem Solving (Mastering Essential Math Skills):](https://thumbs.docslides.com/901218/epub-mastering-essential-math-skills-problem-solving-mastering-essential-math-skills-mastering-essential-math-skills-20-min.jpg)