PPT-CSC 380: Design and Analysis of Algorithms
Author : alida-meadow | Published Date : 2019-06-20
Dr Curry Guinn Quick Info Dr Curry Guinn CIS 2015 guinncuncwedu wwwuncwedupeopleguinnc 9627937 Office Hours MWF 1000am1100m and by appointment Today Quiz 5 due Tuesday
Presentation Embed Code
Download Presentation
Download Presentation The PPT/PDF document "CSC 380: Design and Analysis of Algorith..." is the property of its rightful owner. Permission is granted to download and print the materials on this website for personal, non-commercial use only, and to display it on your personal computer provided you do not modify the materials and that you retain all copyright notices contained in the materials. By downloading content from our website, you accept the terms of this agreement.
CSC 380: Design and Analysis of Algorithms: Transcript
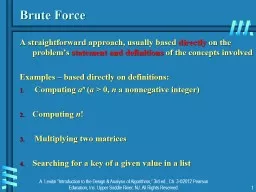
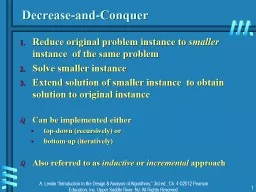
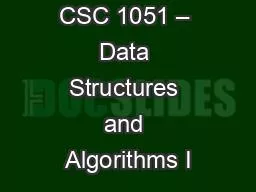
Dr Curry Guinn Quick Info Dr Curry Guinn CIS 2015 guinncuncwedu wwwuncwedupeopleguinnc 9627937 Office Hours MWF 1000am1100m and by appointment Today Quiz 5 due Tuesday night Homework 4 due Thursday night. 1. Brute Force. A straightforward approach, usually based . directly. on the problem’s . statement and . definitions. . of the concepts involved. Examples – based directly on definitions:. Computing . Service India Limited. VLE . Registration Process. To . access any of the services available by CSC, VLEs need to . register. . himself/herself on . apna. . csc. portal by following the registration Process. CSC . Bazaar. CSCs can sell products through this online e-commerce portal enabled through . Infibeam. .. Further CSCs can also open its own online store for free and sell local products through. it. The product can be delivered to the customer either at the CSC Location where the order. 1. Brute Force. A straightforward approach, usually based . directly. on the problem’s . statement and . definitions. . of the concepts involved. Examples – based directly on definitions:. Computing . 1. Brute Force. A straightforward approach, usually based . directly. on the problem’s . statement and . definitions. . of the concepts involved. Examples – based directly on definitions:. Computing . 1. Decrease-and-Conquer. Reduce . original problem . instance to . smaller . instance . of the same problem. Solve smaller . instance. Extend solution . of smaller . instance . to obtain solution to original instance. Dr. Mary-Angela Papalaskari. Department of Computing Sciences. Villanova University. Course website:. www.csc.villanova.edu/~map/1051/. Some slides in this presentation are adapted from the slides accompanying Java Software Solutions by Lewis & Loftus. CSC At a . Glance. Founded in 1970 as a technical support unit for Univac 1108. Reorganized as a company . in 1993, . current. . name. . CSC – Finnish IT Center for Science. , Ltd.. Sole shareholder Ministry of Education and Culture. Dr. Mary-Angela Papalaskari. Department of Computing Sciences. Villanova University. Course website:. www.csc.villanova.edu/~map/1051/. Some slides in this presentation are adapted from the slides accompanying Java Software Solutions by Lewis & Loftus. Dr. Mary-Angela . Papalaskari. Department of Computing Sciences. Villanova University. Course website:. www.csc.villanova.edu/~map/1051/. Some slides in this presentation are adapted from the slides accompanying Java Software Solutions by Lewis & Loftus. Hello BAS Community!. We are excited to provide you with new content on the CSC Portal BAS Page throughout Common Solution. . This proprietary content (available on DOC network) includes: . Real Property Deployment Self-Service Documentation . GS-US-380-1961. . Switch to BIC/FTC/TAF. Design. Endpoints. Primary: proportion of patients with HIV RNA ≥ 50 c/mL at W48 . (ITT, snapshot) ; non-inferiority if upper margin of a two-sided 95.001% CI . MICROSOFT – CSC. Founded in . 1959. . 92,000. . employees . in 92 countries. Global. , . end-to-end capabilities. in consulting, IT and business process outsourcing, and systems integration. $. 16.7 B . Adeetya's Kitchen & Furniture in Pune offers exquisite handmade furniture designs with superior craftsmanship and modern, stylish appeal. https://adeetyas.com/factory-made-furniture-design-in-pune.php
Download Rules Of Document
"CSC 380: Design and Analysis of Algorithms"The content belongs to its owner. You may download and print it for personal use, without modification, and keep all copyright notices. By downloading, you agree to these terms.
Related Documents