PPT-Encrypted Traffic Mining (TM)
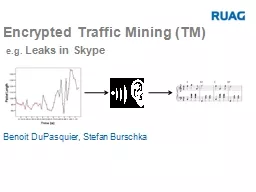
eg Leaks in Skype Benoit DuPasquier Stefan Burschka 2 Contents Who What WTF Why Short Introduction 2 TM Engineering Approach TM Signal Analysis Methods Results Questions
Download Presentation
"Encrypted Traffic Mining (TM)" is the property of its rightful owner. Permission is granted to download and print materials on this website for personal, non-commercial use only, provided you retain all copyright notices. By downloading content from our website, you accept the terms of this agreement.
Presentation Transcript
Transcript not available.