PPT-Physical Randomness Extractor
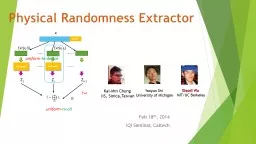
Feb 18 th 2014 IQI Seminar Caltech KaiMin Chung IIS SinicaTaiwan Yaoyun Shi University of Michigan Xiaodi Wu MITUC Berkeley device Ext xs i Extx0 Decouple
Download Presentation
"Physical Randomness Extractor" is the property of its rightful owner. Permission is granted to download and print materials on this website for personal, non-commercial use only, provided you retain all copyright notices. By downloading content from our website, you accept the terms of this agreement.
Presentation Transcript
Transcript not available.