PDF-Protecting Core Industries from Malicious UAS
Author : phillipeshenry | Published Date : 2022-08-09
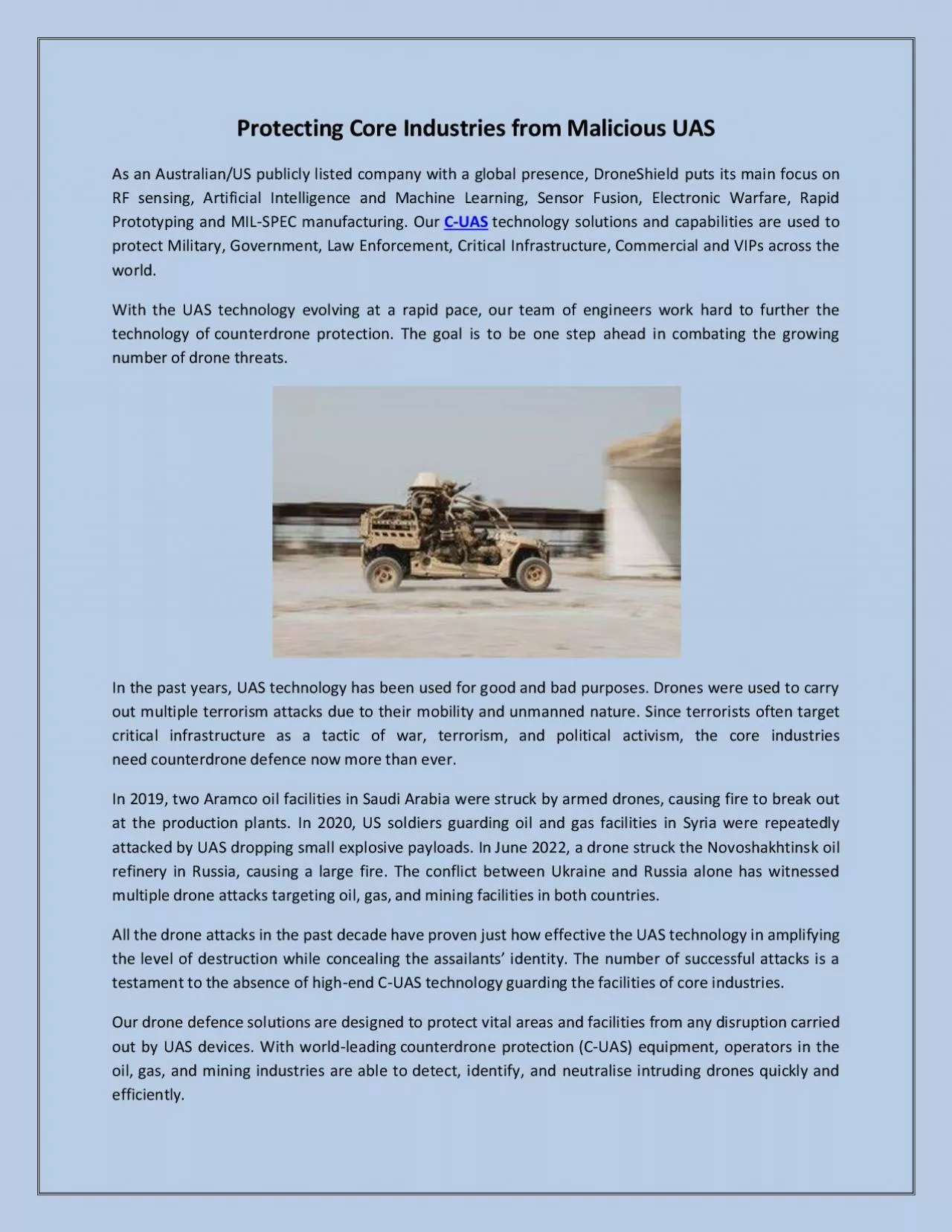
Droneshield is a leader in the design and delivery of mature CounterUAS providing an integrated layered solution from sensing to intercept The Key Considerations
Presentation Embed Code
Download Presentation
Download Presentation The PPT/PDF document "Protecting Core Industries from Maliciou..." is the property of its rightful owner. Permission is granted to download and print the materials on this website for personal, non-commercial use only, and to display it on your personal computer provided you do not modify the materials and that you retain all copyright notices contained in the materials. By downloading content from our website, you accept the terms of this agreement.
Protecting Core Industries from Malicious UAS: Transcript
Droneshield is a leader in the design and delivery of mature CounterUAS providing an integrated layered solution from sensing to intercept The Key Considerations brochure summarises main CUAS concepts when seeking to acquire a solution and generating airspace awareness to detect andor defeat UAS across the military and more Visit now for more detailed information. Three Steps Required:. “Hide” the incompatible group. Do what needs to be done elsewhere in the molecule. Remove the protecting group and return to the original . group. Two protecting groups for alcohols:. Wildlife Conservations. Marise Rodriguez. CAS 100 Section 7. November 13, 2009. It is important to preserve Wildlife conservations because they are beneficial not only to plants and animals but to people as well.. Bahman . Rashidi. December 5. th. , 2014. 1. Overview. Introduction. RecDroid system. Game theoretic model. Nash equilibrium. Discussion. Conclusion. 2. RecDroid system. What is RecDroid?. A framework, to improve . What's . been happening and what’s next. ?. Perth policy forum 18 September 2015. Agenda. Introduction . and . aims. National Framework aims and achievements . Brian Babington, Families Australia . CSH6 Chapter 16. “Malicious Code”. Robert Guess & Eric Salveggio. Topics. Introduction. Malicious Code Threat Model. Survey of Malicious Code. Prevention of Malicious Code Attacks. CSH6. Chapter 16: “Malicious Code”. (UAS aka UAV; Drones). High resolution remote sensing with UAS. Photo by Andrew Xu. Flickr Creative Commons. UAV: Josephat Laboratory, Chiba University, Japan. Learning Objectives. What kinds of UAS are available for remote sensing. . Unmanned aircraft. What is the use of these systems?. . Recreational. Surveillance . Military. Weather observations. USING. . CIVILIAN AIRSPACE. Regulations govern manned aviation (110 years of history). Sarah . Jaffer. PCs monitored by users. Varying levels of security. Autonomous Systems (AS) monitored by . sysadmin. Same security within a system. Which is more valuable in a botnet?. Malicious Hubs. Robbie Hood. Office of Oceanic and Atmospheric Research. 3 November 2010. Reality of Unmanned Aircraft Systems. Proven platforms and payloads . Many classified at Technology Readiness Level – 9. Air Force and Navy Global Hawk - 20,000 flight hours over 10 years. Dr. Steve Koch. NOAA/OAR/National Severe Storms Laboratory. Dr. Bruce Baker. NOAA/OAR/Air Resources Laboratory. July 27, 2016. Needs vs. Requirements. Spatial resolution. (km). Vertical resolution. (m). Employee resourcesThe library Internal newsOur work We are AUS How can we help you Business & Planning Division A Five-year roadmap for the introduction of civil UAS into the National Airspace System ealize What I Was Saying of me teasing me about the clothes Im wearing and the style of music I listen to and stuff like that And I think I just said and it really doesnt sound like me I said You sh iProtecting Students From ExploitationA Legal Guide for Public School Leaders2020 National School Boards Association All Rights Reserved Recommendations for the Near Term . Background. Future success of the drone industry depends on government and private sector funding to support and facilitate the integration and operations of drones in the NAS..
Download Document
Here is the link to download the presentation.
"Protecting Core Industries from Malicious UAS"The content belongs to its owner. You may download and print it for personal use, without modification, and keep all copyright notices. By downloading, you agree to these terms.
Related Documents